Architecture Overview:
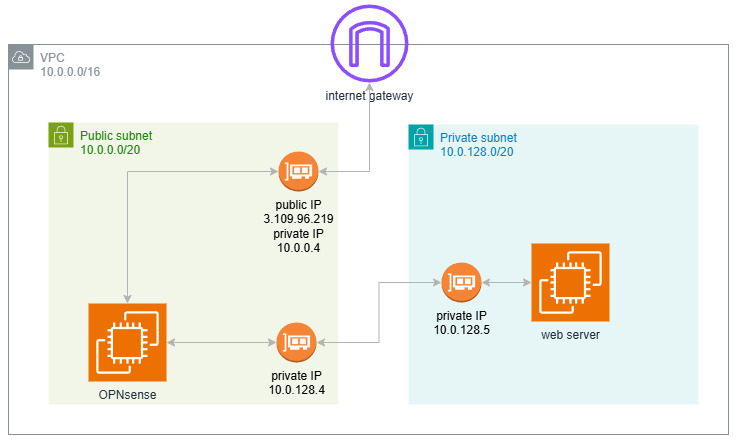
| Interface | Subnet | Private IP | Public IP |
|---|---|---|---|
| WAN (ena0) | test-subnet-public1-ap-south-1a | 10.0.0.4 | Yes |
| LAN (ena1) | test-subnet-private1-ap-south-1a | 10.0.128.4 | No |
- Launch OPNsense EC2 Instance (WAN only)
- Go to EC2 → Launch Instance
- Choose your OPNsense 25.1 Nano AMI
- Under Network Settings:
VPC: Your existing one
Subnet:test-subnet-public1-ap-south-1a
Auto-assign public IP: Yes
Click Advanced network configuration
Assign Private IP:10.0.0.4 - Security Group:
Allow inbound:443(HTTPS – for Web GUI)
⚠️ Do not attach the LAN interface yet — we’ll do that later.
- Access EC2 Serial Console
- In EC2 Console → Instances → Select your OPNsense instance
- Click Connect → EC2 Serial Console
- Login:
Username: root
Password: opnsense
- Edit
/conf/config.xml(Enable Public WebGUI Access)
vi /conf/config.xml
Insert the following inside the <webgui> section (or create one if missing):
<nohttpreferercheck>1</nohttpreferercheck>
<nodnsrebindcheck>1</nodnsrebindcheck>
- Reboot the Instance
reboot
- Access the OPNsense Web GUI
Open a browser and go to:
https://OPNsense-public-IP
Login
Username: root
Password: opnsense
- Create & Attach LAN Interface (ena1)
- Go to EC2 → Network Interfaces → Create Network Interface
Subnet:test-subnet-private1-ap-south-1a
Private IP:10.0.128.4
No public IP - Attach it to the running OPNsense instance
- Assign & Enable LAN in OPNsense
- Web GUI → Interfaces → Assignments
- Assign the second interface as
LAN - Set static IP:
10.0.128.4(OPNsense LAN IP) - Enable the interface
- (Optional) Confirm LAN Firewall Rule
OPNsense typically includes this default rule:
IPv4 * LAN net * * * * * Default allow LAN to any rule
If present, no action needed.
If missing, add this rule:
- Go to:
Firewall → Rules → LAN - Add:
Action:Pass
Source:LAN net
Destination:any
Description:Allow LAN to any rule
- Update Route Table for Private Subnet
Go to VPC → Route Tables, find the one associated with test-subnet-private1-ap-south-1a and:
Add a route:
Destination: 0.0.0.0/0
Target: 10.0.128.4 (OPNsense LAN IP)
Now all instances in the private subnet route outbound traffic through OPNsense.
- Disable RAM Disk
- Login to the OPNsense Web UI.
- Navigate to:
System → Settings → Miscellaneous - Scroll down to the section:
“Disk / Memory Settings (reboot to apply changes)” - Uncheck these options:
Use memory file system for /var/log
Use memory file system for /tmp - Save
- Reboot the firewall to apply the changes.